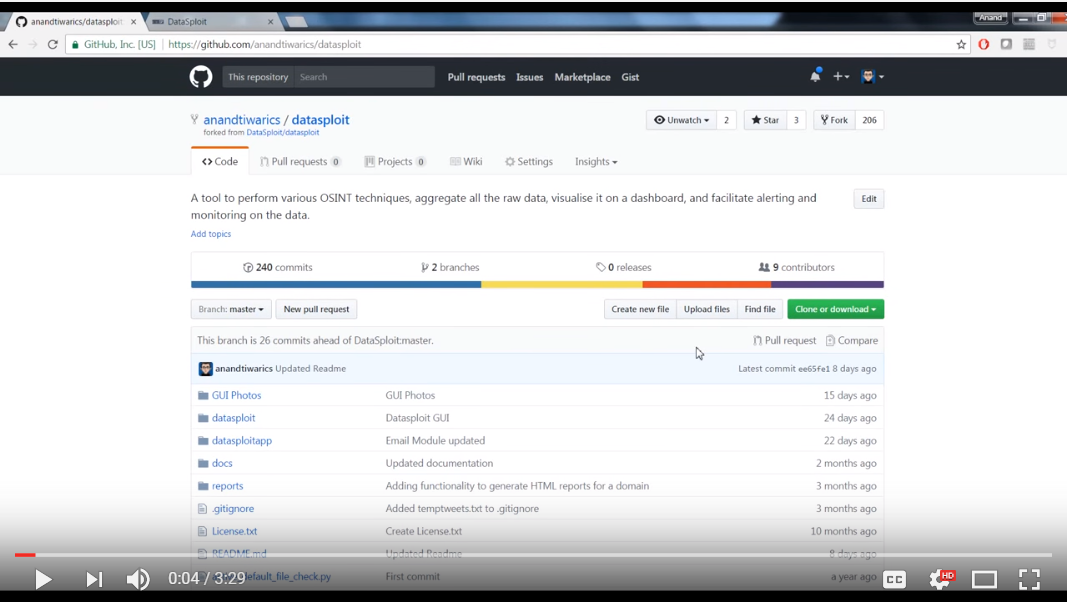
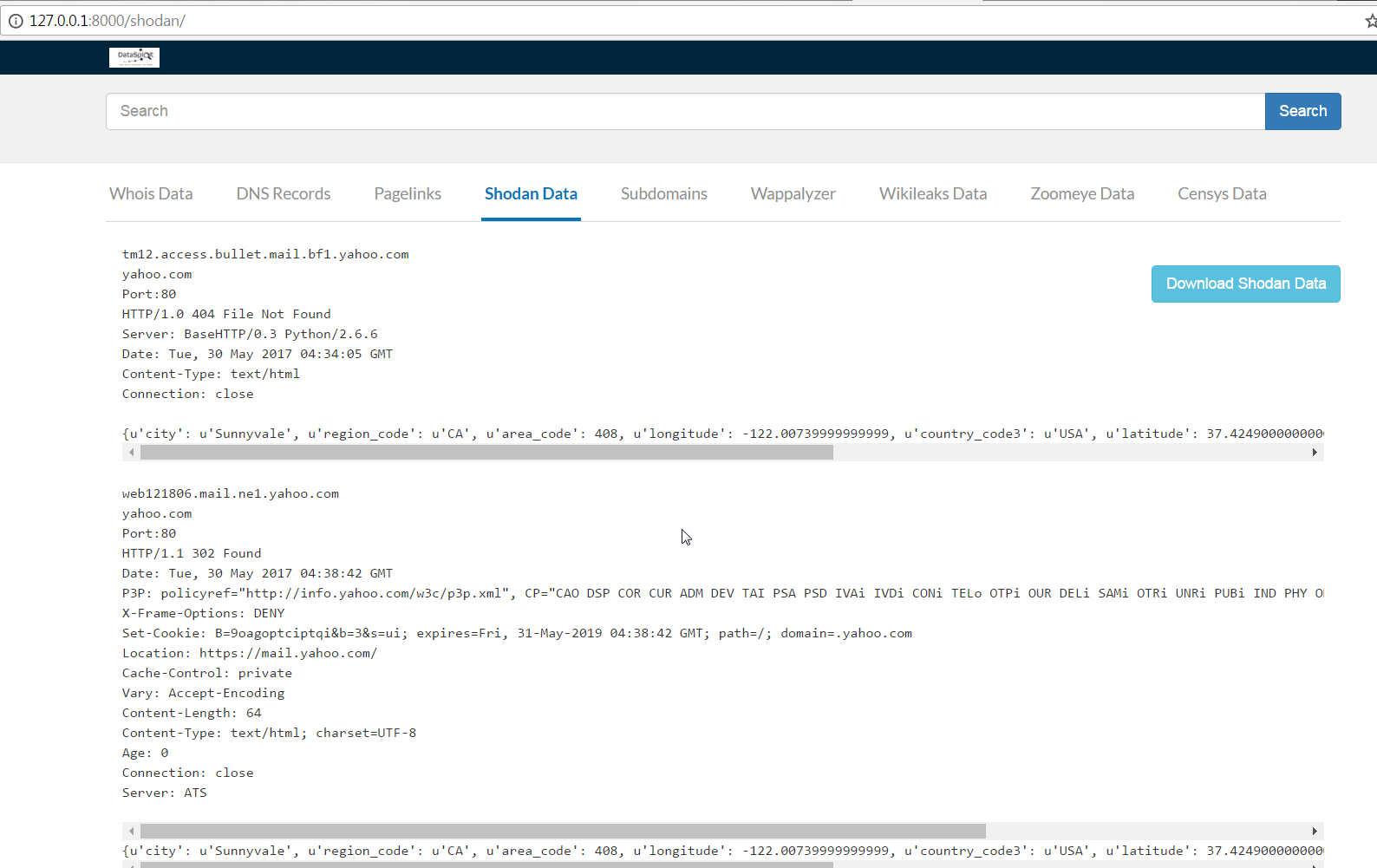
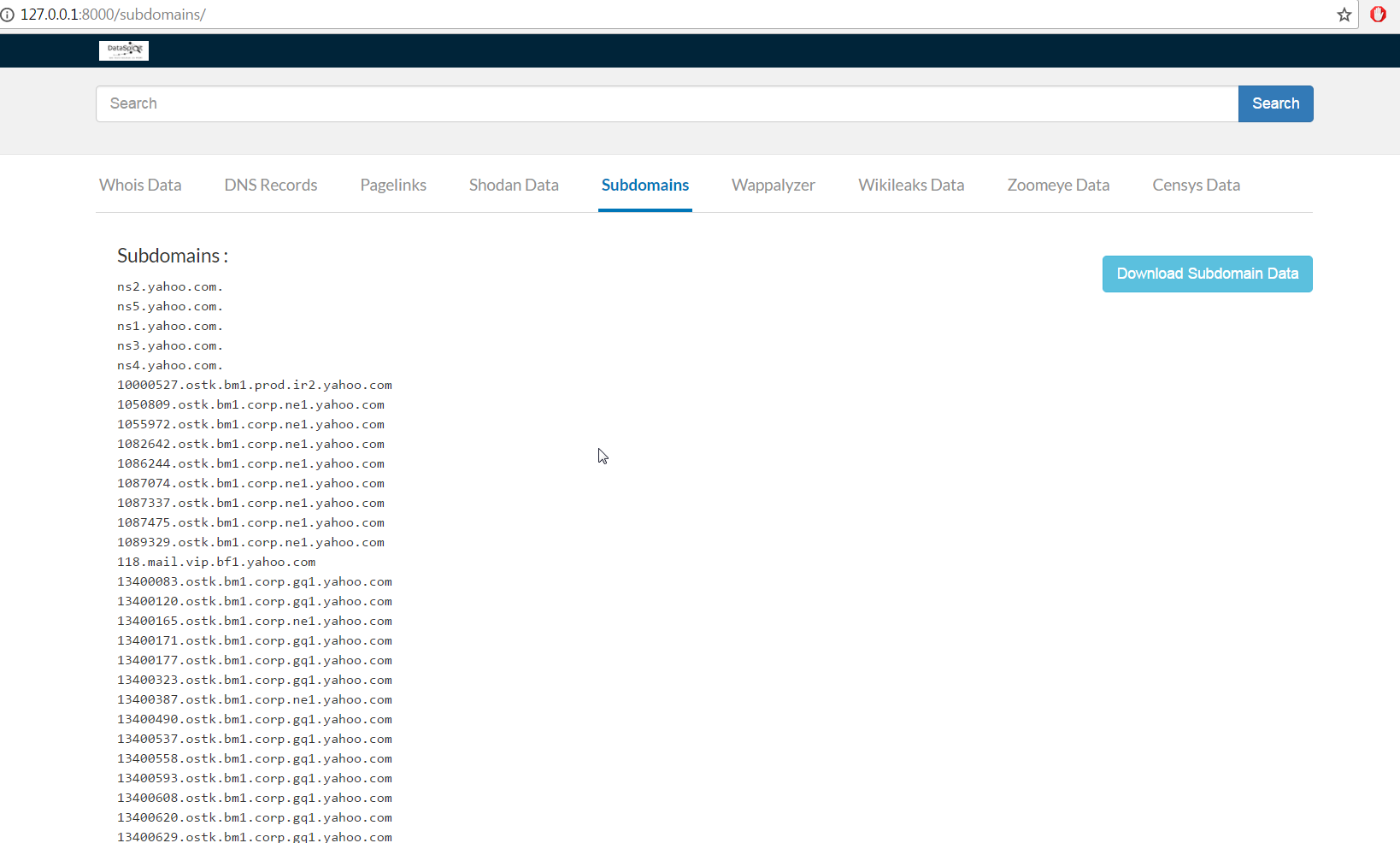
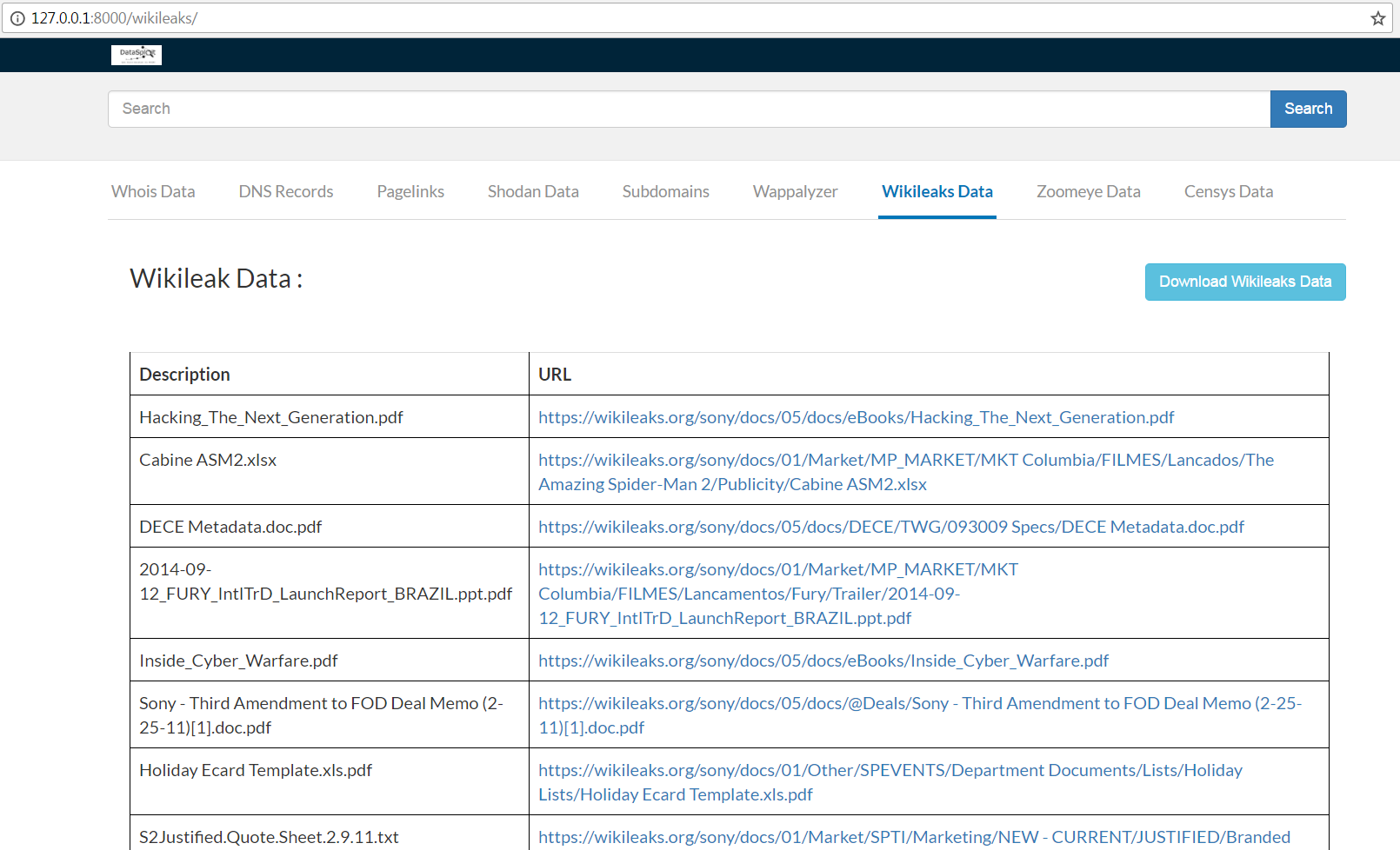
- Performs OSINT on a domain / email / username / phone and find out information from different sources.
- Correlates and collaborate the results, show them in a consolidated manner.
- Tries to find out credentials, api-keys, tokens, subdomains, domain history, legacy portals, etc. related to the target.
- Use specific script / launch automated OSINT for consolidated data.
- Performs Active Scans on collected data.
- Generates HTML, JSON reports along with text files.
____/ /____ _ / /_ ____ _ _____ ____ / /____ (_)/ /_
/ __ // __ `// __// __ `// ___// __ \ / // __ \ / // __/
/ /_/ // /_/ // /_ / /_/ /(__ )/ /_/ // // /_/ // // /_
\__,_/ \__,_/ \__/ \__,_//____// .___//_/ \____//_/ \__/
/_/
Open Source Assistant for #OSINT
website: www.datasploit.info
Usage: domainOsint.py [options]
Options:
-h, --help show this help message and exit
-d DOMAIN, --domain=DOMAIN Domain name against which automated Osint
is to be performed.
- Python 2.7 (because bunch of dependencies do not support Python 3.0)
- Bunch of python libraries (use requirements.txt)
pip install -r requirements.txt
python manage.py collectstatic
python manage.py makemigrations
python manage.py migrate
python manage.py runserver